BS Gabon and its
Cisco and Westcon partners
co-hosted an event on Tuesday, March 29, 2019
at the Radisson BLU Hotel
to showcase Cisco’s new products
security of data centers and associated security products.
As a reminder, the working environment of companies is in transition
state-of-the-world Datacenter and Cloud. This transition requires
automation of security strategies and provisioning of security
applications dynamically.
Most of today’s Datacenters continue the manual approach to setting up their policy security and provisioning.
Through this event, BS Gabon and its partners wanted to share their experiences of designing a fully secure data center and providing full visibility of the data users, devices, networks, apps and Process.

Why conventional security solutions don’t don’t always work.
Data center administrators face significant challenges. They need to secure new environments without compromising its performance or operation. For secure the data center, the solution must:
Provide visibility and control over custom data center applications
Manage asymmetric traffic flows and traffic flows application transactions between devices and data centers
Adapting to the evolution of data centers: virtualization, software-defined network (SDN), virtualization of (NFV), Cisco’s application-based infrastructure (ACI) and more than Still
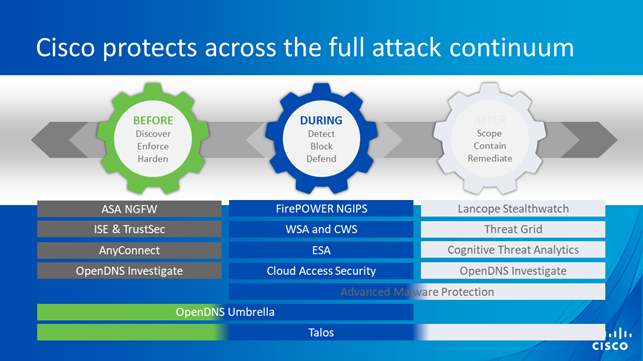
Be effective at every stage of the attack: before, during and after
Integrating with deployed security features all over the network
Take charge of deployment and traffic between geographically dispersed data centers, including environments cloud, public and private

The first victim of compromise: the data center
Many modern cybercriminal campaigns are specifically designed to help hackers reach the data center, where valuable data such as customer data, personal data, data, data, data, data, data, data, financial information and the company’s intellectual property. But protecting the data center is a challenge. At the same time, data center evolves: from the physical to the virtual, to new environments such as NDS and ACI infrastructure. Data center traffic is already growing exponentially, mainly due to the growing use of the cloud and the emergence of cloud environments Internet of Things (IoT).
Today’s data centres already provide a a wide range of applications, services and solutions for businesses. Many of them rely on services deployed in data centers geographically dispersed to manage their growing needs for cloud computing and traffic.
Another complication for data centers and their teams: the limits of provisioning and performance affects the deployment of security solutions such as next-generation firewalls, and prevent inspection of the entire Traffic. Safety should not be ensured at the expense of the performance of the data center. In today’s data center, the provisioning of a security solution must be completed in a matter of hours, or even within a few Minutes. It should not take days or weeks. Performance must evolve dynamically so that it is possible to manage large traffic spikes.

Secure the data center in five steps
The complete protection of the data center requires enhanced security in five key areas. The solution must:
1. Provide visibility and control over custom data center applications.
2. Manage asymmetric traffic flows and traffic flows application transactions between devices or data centers
Many new-generation firewalls are unable to secure asymmetric traffic. Security solutions dedicated to the data center must also manage application transactions between data centers or devices, including virtual devices
3. Adapt to the evolution of data centers. The data center environments are moving from the physical to the virtual, to the models of SDN, ACI infrastructure and next-generation NFV.
4. Be effective at every stage of the attack: before, during and after. Conventional approaches to security offer only a limited detection of attacks and limited visibility in the environment Data center; they focus mainly on protection perimeter level. To cover the full spectrum of attacks, it is a question of prepare for very variable angles of attack: network, terminals, terminals mobile and virtual environments.
5. Protect the entire network. All the solutions data center security must take into account the needs of users connect directly to critical resources in a data center.
The security of the data center is different.
To truly protect the modern data center new data center models, companies can’t to settle for a new generation firewall. They need to adopt a comprehensive and integrated security strategy, as well as an architecture providing seamless and intelligent protection across the network distributed, from the periphery to the data center, to the cloud, without harming performance.
Securing the modern Cisco data center offers powerful tools to protect data center environments in the middle of today’s evolution, not just their periphery. The solutions Cisco® ASA (Adaptive Security Appliance) for the safety of the data center are designed to protect physical and virtual environments and allow companies to seamlessly migrate from a data center new generation classic to make long-term deployments, protect investments and ensure the full protection of the data center. The new elements of the Cisco ASA platform are:
· The Adaptive Security Virtual Appliance (ASAv): virtual version of the full set of features of the Cisco firewall Asa
· The Cisco ASA 5585-X with features FirePOWER: Security appliance specially designed for the data center, fully supporting traditional data center environments, SDN and ACI, the Cisco ASA 5585-X Adaptive Security Appliance with FirePOWER features has advanced firewall and firewall features next-generation IPS security.
· The new intrusion prevention system (NGPIS) Cisco FirePOWER: market leader in NGIPS, FirePOWER is available in the form of physical or virtual solutions. It identifies and evaluates connections to data center resources, and monitors suspicious activity on the network.

Other Cisco solutions provide protection data center:
· Cisco ISE (Identity Services Engine) and TrustSec: IT teams can create, share and implement IT policies dynamic security in the event of new devices or new devices being added users in the data center environment via UCS Director.
· Cisco OpenAppID technology for Snort: IT teams can create, share and implement a mechanism detection of applications and develop specific rules for custom applications from the data center.
· Cisco FireAMP™ and FireSIGHT™: a advanced analysis and protection against malware are necessary when a holistic, attack-based approach is to secure the modern data center before, during and after a Attack.
And other solutions that had been the subject of a very constructive sharing with the participants of the event.











